A Story of Data, Bitcoin, and Other Cryptocurrencies Trading Cryptocurrencies: Are You In? If...
Cryptocurrency Security Issues
With the rise in value of Bitcoin (currently $10701.69 / BTC as I write this) the interest in cryptocurrency has never been higher. One of the most fundamental issues with any cryptocurrency is transparency and security. How can you protect your assets? How can you ensure that no one else can spend your tokens? This post will dive into some of the basics of cryptocurrency as well as things you need to know in order to protect yourself while exploring this new type of digital asset class.
Introduction - Blockchain
What is all of this? Wallets? Blockchain? Private keys?
The blockchain: We have heard a lot in the news about the blockchain, and how it will transform everything from banking to travel to buying groceries. But what is a block chain? What benefit does it provide?
At it's most basic level, cryptocurrency can be thought of as a digital representation of an asset whose entire history is stored on a public ledger that anyone is able to see. This ledger is the authoritative source for the history of any token. If you have the ability to track a token from creation to the current point in time, then you can derive the current amount of a token that a particular person has. Another name for this ledger is the blockchain. Each block contains transactions as well as a pointer to the previous block, so if you were to line them up end to end, you would have a chain of blocks. An example may make this more clear.
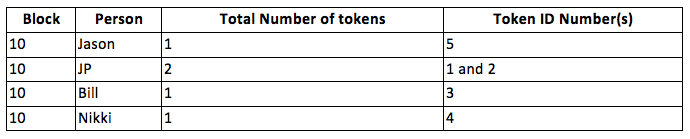
Assumption: In block 9, someone transferred Jason 5 tokens, no one else had any tokens at this point in time. Here is what block 10 would look like.
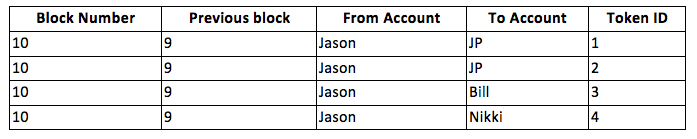
So, the balances of everyone according to block 10 look like this.
Wallet
Cryptocurrency is stored in a digital “wallet”, which is how Jason will see that he has 1 token, and JP will see that he has 2 tokens. The wallet is a piece of software that interacts with the public ledger in a very defined way and contains the secret key of the address associated with your wallet. The wallet is secured by something called the private key. This key is something that only you have, and no one else is every supposed to know. The private key is required to authorize any transfer of tokens out of your wallet to someone else's wallet. This is the exact same concept as within Public Key Cryptography.
Security Issues
"If you don't control the private key, then you don't control the wallet."
The above is probably the most important thing to know about digital wallet security. If you don't control the private key, then you don't have the tokens. To make things easy on the non-technical public, there are a number of web services that will provide a cryptocurrency wallet, but unfortunately the private key to that wallet remains under their control. This means that you are at risk for a number of things.
• Security Breach - If a malicious actor breaks into the security of that site, then they can transfer away all of your tokens, and there is nothing you can do about it.
• Exit Scam - If the people who run the website decide to just shut the doors, and turn off the lights, then you no longer have access to your tokens. Since they have the private key to your address, then they have the ability to spend your tokens.
• Poor Customer Service - If you have a problem logging into the website, and they don't have enough staff to handle things like this, or no way to truely identify you, then you may lose access to your tokens.
To protect yourself, you need to maintain control of the private key at all times. One of the ways to do this is to install the wallet software for the cryptocurrency on your own local computer. This way you are the only one with access to the private key, and by extension, you are the only one that can send tokens out of that particular wallet. This of course brings it's own set of issues such as making sure that your computer is secure.
A different and currently the safest way to protect your private key is with a hardware wallet. This is a device that is about the size of a USB stick, plugs into your computer only when you need it, and uses a passphrase that you enter on the device to “unlock” your private key. When you are done interfacing with the wallet, then you unplug the key, and put it back into your safe. This ensures that even if your computer is compromised, that the attacker still will not be able to spend your tokens, since they will not have access to the private key associated with the account.
This is just a brief overview of one of the largest security concerns with using cryptocurrencies. At their core, all of the various cryptocurrencies work off this same principle. You have a wallet (an address) that is tracked via the public ledger (blockchain). In order to transfer tokens out of your wallet, you must provide the private key. Your wallet can be stored on a web-site that does this for you when you log in, or if you take your security seriously, then you maintain it on your own computer or via a hardware device specifically designed for this purpose.