Optimizing Costs and Eliminating Excessive Alerts by Combining Splunk and STEALTHbits Introducing...
5 Ways to Use Splunk for Security
I’ve Got Data, Now What Do I Do with It? Converting Machine Data into Practical Security Insights
From Machine Data to Security Insights with Splunk
Your run-of-the-mill security ecosystem just isn’t going to cut it in the domain of modern cyberattacks. These days, we’re all facing significantly more sophisticated attack methods and a slew of potential threats from numerous sources. Reacting to security events is no longer an option. Rather, business risk has to be managed continually and security strategies must be proactive. This includes making use of security analytics, Splunk explained, which means collecting data from both security and non-security sources to get a more comprehensive view of what’s going on in your environment.
With Splunk, you can use machine learning and behavioral analytics to augment the effectiveness of your security teams. Your analysts will be far better equipped to identify, investigate, and respond to threats. While the short-term goal is to collect the data that matters most for your use cases, the ultimate impacts are ample:
- Gain all-encompassing security analytics from both security and non-security data sources
- Restructure advanced threat investigations using a kill chain methodology
- Execute fast incident analysis with quick time-to answer plus proactive threat hunting
- Use machine learning-based advanced analytics for efficient anomaly and threat detection while mitigating insider and external threats
- Adaptive response to improve operational efficiency with automated and human-assisted decisions
5 Ways to Use Splunk for Security
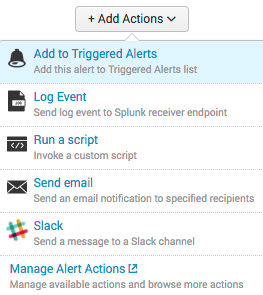
So let’s get down to it. If you’re just getting started with making use of your machine data for the greater security good, where do you start? Splunk Security Essentials is a free app that highlights over 55 working examples of anomaly detection. Here are just a few essentials:
1. Email logs
Phishing is a risk running rampant, but fortunately, there are additional tactics you can use other than employee training to put yourself in a better position of defense, including feeding email logs into Splunk.
- Look for emails from outside your organization with the company domain. One of the most common phishing and fraud methods for a malicious actor is using your company domain to make email look official when it’s actually coming from somewhere else. When you send emails through code, it’s possible to specify the domain freely. Behind the scenes, you can see what IP address emails came from, and use Splunk to set up alerts when something suspicious comes through.
- Emails with lookalike domains are another common phishing tactic. Some attackers will switch easily mistakable letters, or use a believable subdomain (such as .help.com, .support, etc.) You can also set up an alert for these types of emails to avoid successful trickery.
- Spikes in password resets are potential indicators you’ll want to be aware of.
- Users with an increase in outgoing email should be monitored. If a malicious actor has successfully hacked a user’s computer, a virus could be sending information back to the individual who created it using email.
2. Windows system logs
- Authentication against a new domain controller: a common indicator for lateral movement is a user logging into new domain controllers. Create an alert that will tell you any time there’s a new authentication on a different controller.
- Significant increase in interactively logged on users is always worth looking into, and Splunk Security Essentials includes a search you can implement that will look for systems with dramatically more logins than is typical with a per user baseline.
- Any account activity from a disabled account should be flagged. It’s common for businesses to forget to cancel emails for contractors or old employees, so triggering an alert for those logs comes in handy, too.
There are a myriad of use cases for Windows system logs alone, so remember that your use cases depend on what’s most important to your business and security team.
3. Firewall logs
- Anytime source IPs in your environment are communicating with more hosts than normal, this will typically detect if there’s any sort of scanning activity or lateral movement. Splunk can determine a baseline of IPs and alert on anomalies.
- Sources sending out DNS or ping requests and embedding data into the payload. If you’ve been compromised, a malicious actor can send out ping requests and embed whatever information they want. This is often not logged because it’s something that’s hard to find, but using firewall logs, you can alert on it.
- Sources sending out high volumes of DNS traffic, which is fairly similar to the above. Another common method for exfiltration is creating large volumes of DNS or ping requests and embedding data into those payloads.
4. Print logs
- Users who are printing a lot more than normal are worth keeping an eye on in case of a potential insider threat.
5. Custom-in house apps
- In general, if you have any custom apps, you should definitely pull those logs in. Specific use cases are dependent upon your situation, but building baselines of activity such as failed log-ins and common activity, plus alerting on anomalies is a good building block.
BONUS: Make sure to also send your syslog from routers and switches into Splunk, gaining visibility into the network traffic moving throughout your environment.
Identifying the Right Use Cases for You
The need for visibility into your IT operations has increased dramatically as environments become more widespread and cloud services and applications are adopted increasingly. Splunk is a great way to gain a broader view of activities to give your security team a leg up on suspicious activity.
Feeling overwhelmed with where to start, or need assistance identifying the best use cases for your business? You can use Splunk for security and here at August Schell, we can help. Get in touch with us today, or call us at (301)-838-9470.
 Are you having an issue on-boarding data with Splunk?
Are you having an issue on-boarding data with Splunk?
Does your Splunk seem to underperform? Are you having trouble scaling?
We're here to help.



